As you know, NIST’s Cyber Security Framework (CSF) was originally configured for public institutions and private companies in the United States. However, it has been positioned itself by wide-ranging and worldwide implemented. In this article, we will examine how a category within NIST supports each other and how to convert each one to a process to get an acceptable level of cybersecurity in the organization. You may see other articles about NIST’s CSF in my blog.
Figure 1: NIST Cybersecurity Framework Main Domains / Functions

Each category of NIST CSF should be operated as a process to ensure cyber security at the expected level in the organization. Structuring security processes within this framework will provide assurance to cyber security officers, employees, stakeholders and shareholders for the institutional, successful and sustainable level of security. NIST’s Cybersecurity Framework Category List has been summarized as a list below. (see Figure 2)
The Figure below is a small view of the Identify Function with its categories:
Figure 2: NIST Cybersecurity Framework Category List
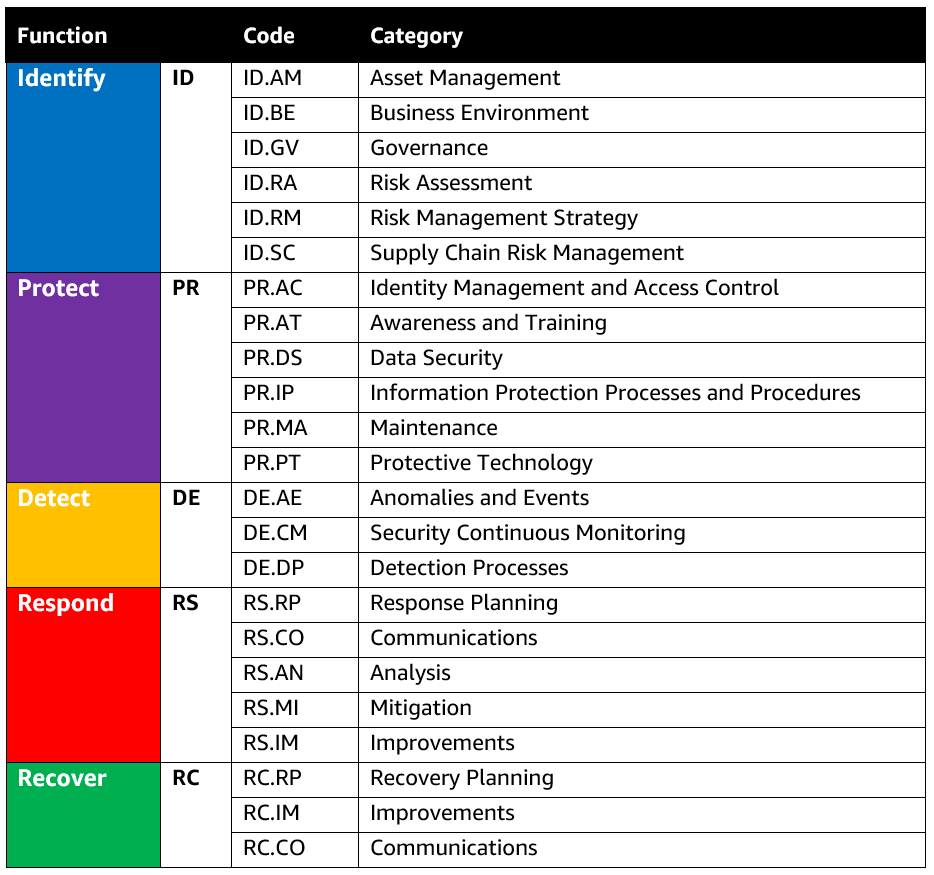
The five main functions in NIST CSF point to each phase in ensuring to provide expected level of cybersecurity. There are many cyber security categories that support each other between these phases (See Figure 2). The categories here need to interact with each other for a healthy and sustainable cyber security structure. Each category should be dealt with as a separate process. The inputs of each process, the transactions within the category and the outputs obtained as a result of these transactions should work in harmony with each other by feeding the other processes.
You can examine the process diagram that I have created about how the categories within the NIST Cybersecurity Framework can be used as a cybersecurity process and how these processes support each other in Figure 3 and you can benefit from the relationships here in your corporate processes.
Figure 3: NIST Cybersecurity Framework Process Diagram
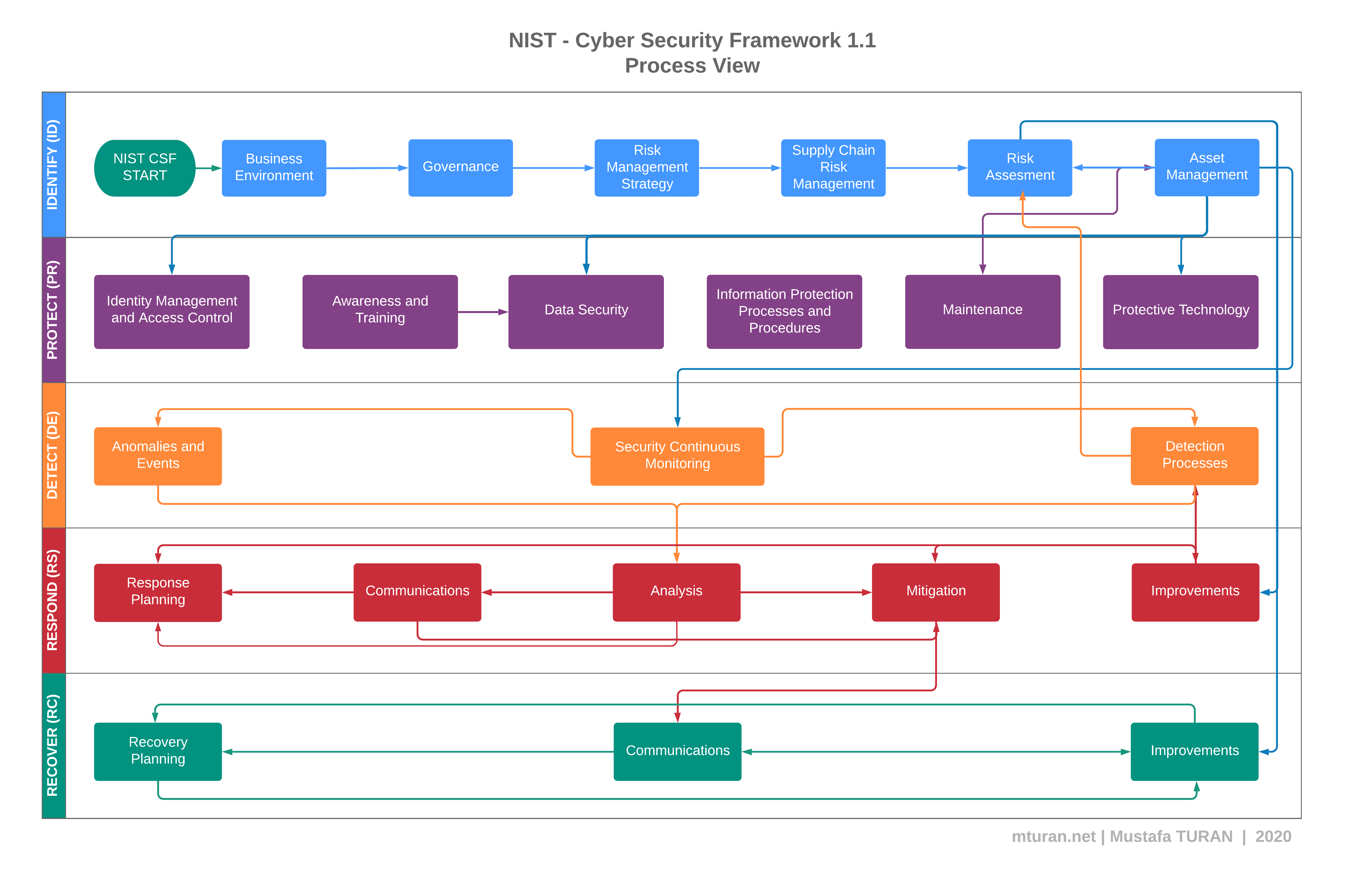
Click here to reach of the full size version.
Did you enjoy this blog article? Comment below with your feedback.
Regards,
Mustafa TURAN